STIR/SHAKEN as a Service
STIR/SHAKEN as a Service - is a standards-compliant solution providing real-time caller authentication (signing), verification, and certificate repository services. It is comprised of the following:
- Secure Telephone Identity - Authentication Service (STI-AS) and the associated functions of Service Provider Key Management Service (SP-KMS) and Secure Key Store (SKS) to process originating network requests for signed assertion of caller’s identity
- Secure Telephone Identity - Verification Service (STI-VS) and the associated function of Secure Telephone Identity Certificate Repository (STI-CR) to process terminating network requests for certificate verification of a caller’s identity.
- Secure Telephone Identity – Certificate Authority (STI-CA) providing the following capabilities:
- Accept SHAKEN Certificate Signing Requests (CSRs) for new certificates
- Automatically validate Service Provider Code (SPC) Tokens and issue standards-compliant SHAKEN signing certificates that include the required Telephone Number Authorization List extension.
- Revoke certificates if needed and notify the Secure Telephone Identity – Policy Administrator (STI-PA)

Reputation Scoring Service

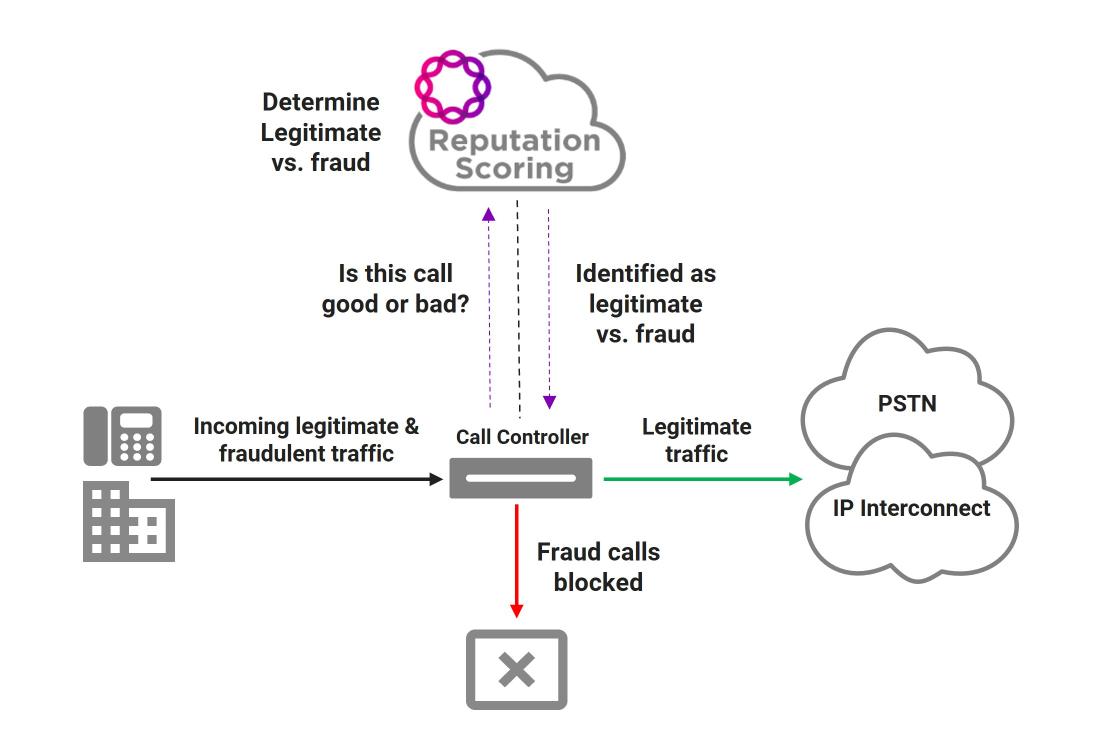
Reputation Scoring is used for to prevent telephony fraud and to mitigate originating or terminating robocalls.
Reputation Scoring provides the following, in real-time, on a per-call basis:
- Fraud Scoring - provides one or more reputation scores indicating the likelihood of a call being fraudulent based on Ribbon-supplied databases, STIR/SHAKEN verification outcome, in-network fraud insights from Ribbon Analytics, and customer-provided data sources such as allow lists, deny lists, fraud lists, and do-not-originate lists.
- Nuisance Scoring - provides one or more reputation scorse indicating the likelihood of a call being a telemarketing or nuisance call based on Ribbon-supplied databases and STIR/SHAKEN verification outcome.
- Call Validation Treatment - provides guidance on how a call should be handled, based on the reputation scores associated with an given call.
Originating Robocall Mitigation
To prevent robocalls from originating on a voice service provider's network, a query is made to the Reputation Scoring service for every call attempt, to determine the likelihood that a call is illegitimate and should be blocked. The query made be done using SIP messaging or a REST API.
A call will be considered illegitimate for two reasons:
- If the originating number is being spoofed using a Telephone Number that shows up on a Do-Not-Originate list or is an unallocated, unused, or invalid number.
- If reasonable analytics indicate the call is highly likely likely to be illegitimate and malicious in intent.
If the call is determined to be illegitimate a the response back to the originating call controller/switch will be to block the call, otherwise the originating call controller/switch will be instructed to route advance the call based on normal routing.
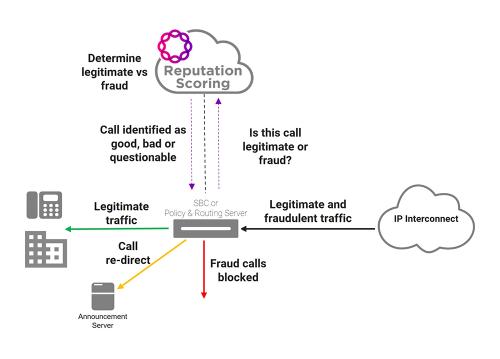
Terminating Robocall Mitigation
To prevent robocalls from terminating on a voice service provider's network, a query will be made to the Reputation Scoring service for every call, prior final call disposition, to determine the likelihood that a call is illegitimate and should be blocked or is likely legitimate and should be allowed to proceed normally. Unfortunately, many calls may have reputation scores that fall somewhere between these two outcomes and should be given special call validation treatment options. Some examples of call validation treatment options are:
- Route to an announcement indicating the call cannot be complete at this time
- Divert to a voice mail system
- Route to a "CAPTCHA" system that will play an announcement asking the calling party to respond to instructructions, such as entering a specific set of digits, if they want the call to proceed.
- Alter the Calling NAMe (CNAM) display to "Potential SPAM" to let the terminating party know so they can make a decision to answer or not answer a call
Ribbon Identity Hub
Ribbon Identity Hub is a cloud-native SaaS platform that enables Ribbon’s hosted identity assurance services. It has been designed to leverage cloud-native, webscale technologies to deliver a highly scalable, highly reliable, extremely flexible solution that is fully adaptable to any service provider's traffic patterns.
Delivering identity assurance services outside of the traditional call processing infrastructure means a service provider can be responsive (in days or weeks) to the dynamic nature of fraud and robocalling as bad actors continuously adapt to stay one (or two) steps ahead of the service provider community.
Identity Hub supports both configured and dynamic machine learning (ML) models for identity assertion and reputation scoring, based on multi-source data integration. With insights into service provider network topology and identification of fraud or robocall traffic patterns by Ribbon Analytics, Identity Hub inference can dynamically adapt to new network conditions and traffic patterns to improve the accuracy of call classification.
A key attribute to Identity Hub adaptability is its design as an open ecosystem, with open APIs and open data integration. Identity Hub incorporates a service graph function that can be easily configured to define how it ingests and processes real-time and non-real time data from other services or databases. The service graph function also provides a flexible way to integrate current and future services based on customer specific sequencing and flows.
Examples of Ribbon Identity Hub open APIs and open data integration are:
- Real-time integration of 3rd party transactional policy information, such as real-time attestation of caller identity from Ribbon STI or Calling Name (CNAM) databases
- Ability to collect or accept non-real time, 3rd party policy data that can be crowdsourced, carrier-based, or subscriber provided
- Accept near-real time data on potential robocall and fraud, from Ribbon Analytics or any 3rd party customer analytics solution, based on analysis of network traffic patterns and Call Detail Records for every call
- Accept requests from Ribbon or 3rd party solutions for reputation scoring, call signing or verification
- Ability to provide reputation scores, STIR/SHAKEN attestation or verification responses, and call validation treatment options to a variety of Ribbon and 3rd party network elements
Ribbon Identity Hub services are invoked in real-time, meaning they are in the call path for each call. Because of this, Ribbon Identity Hub is designed to deliver real-time processing with very low latency in a highly robust and reliable architecture.