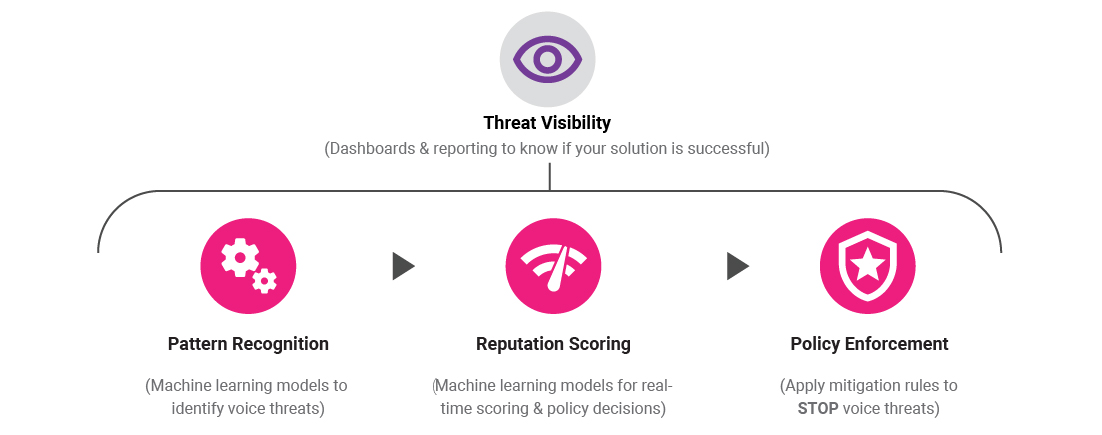
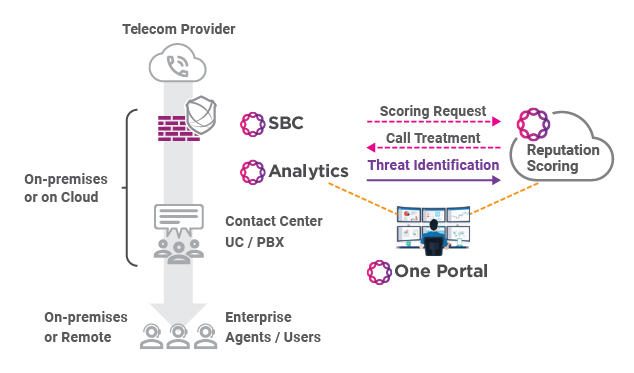
With the potential for malicious attacks via SIP and VoIP, security for unified communication (UC) and Contact Center (CC) infrastructure and services requires a solution designed specifically to address these unique attack vectors. Leveraging the value of behavioral analytics and machine learning models, it is possible to detect potential illegal robocalls, fraud and TDoS attacks. By incorporating this information into a cloud-hosted real-time assessment and scoring service, it is possible to determine the reputation of each and every call. Policy decisions can be made in real-time and policy enforcement will prevent these voice threats from disrupting your business. Policy enforcement is done in real-time at session border controller(s) on a per session basis to drive an overarching security umbrella that greatly reduces the SIP/VoIP threat landscape.
Ribbon's voice threat prevention solution is a based on analytics and machine learning models within FraudProtect and within Ribbon's cloud-hosted Reputation Scoring service.
Reputation Scoring Service
Ribbon's cloud-hosted service uses machine learning models to provide real-time multi-dimensional scoring, based on local and national data sources. Reputation score(s) indicate the likelihood that a call is being made with malicious intent. Using this information and policy decision guidelines, a decision can be made for each and every call that will indicate the optimal call validation treatment to ensure good calls are handled normally while illegitimate robocalls and telephony fraud attacks are blocked before they cause damage.
Using Session Border Controllers for Policy Enforcement
Once a call validation treatment is identified, real-time policy enforcement is possible. For any enterprise using IP-based Unified Communications or Contact Centers, the ideal policy enforcement point will be a session border controller. Ribbon provides a suite of SBCs that can fulfill this role