Finding Real-Time Communication Threats Resembles a Game of Word-Search
We have all presumably played word searches. Spotting specific words among a litany of letters can be difficult and in some cases, downright frustrating if you have a huge set of words to find. It is a game of patience, visual acuity, and a methodical review of the letters.
This is a great analogy for detecting real-time communication (RTC) attacks because it can be very hard to detect attacks in an RTC network (i.e. SIP network) with all the data that you have to filter through to get to the right answers. Otherwise you may get a number of false positives when trying to detect threats against your RTC network. Thus, the reason this analogy is so important.
Here at Ribbon, we think RTC threat hunting involves the anomaly detection process of searching through mountains of data from RTC networks and infrastructure for coordinated / advanced RTC threats that are evading existing security solutions and defenses such as your SBCs and FWs.
And, even though SBCs, firewalls, intrusion prevention solutions, etc., are all designed to detect and protect against threats coming in through that particular network device, I like to say that “RTC threat hunting” is the layer above these networks devices. A bird’s eye view of what threats or anomalies are actively running in my network that my individual network devices are missing and how I can find them.
So RTC threat hunting is much like a word search game. You know the words exist, you know you must look forward, backwards and diagonally, but you cannot always find all of them.
Similarly, when hunting RTC threats you may not know what the threats actually are, but it is a safe assumption to say bad actors are doing something wrong or staging to do something malicious in the future. If you can find those hidden “threats,” you can win the game.
If you think of the problem, puzzle, or game with clear objectives and leverage the tools you have today …could you detect an RTC threat spanning across your entire RTC network? RTC threat hunting is much more than a correlated black box report or an alert.
RTC threat hunting requires you to dig in deep, use a magnifying glass, to help find the threat. Having RTC security best practices to begin with is an absolute requirement for success, since everything you do for threat hunting depends on it. And, looking at new strategic approaches such as big data analytic toolsets for RTC security is the only way to ultimately stop bad actors from wrecking havoc in your RTC network.
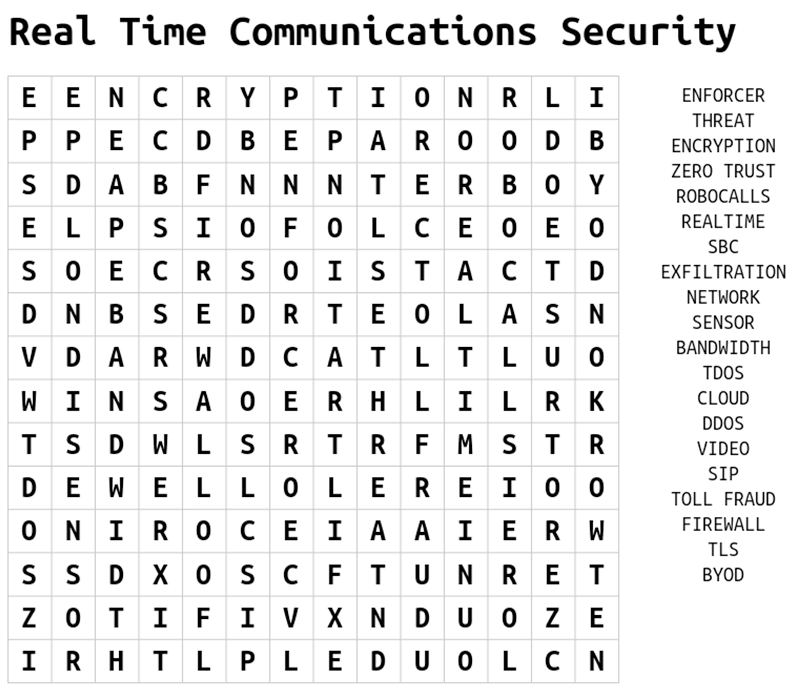
While you are letting this all sink in, below is fun and easy word search puzzle for you to print out on real-time communications security. And when your done with that, click the hyperlink to learn how Ribbon’s Protect platform can help you detect, predict, respond and prevent security threats in your RTC network.
Play this puzzle online at: http://thewordsearch.com/puzzle/399526