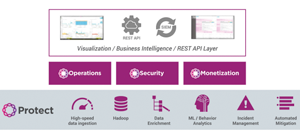
Operations, Security & Monetization Applications
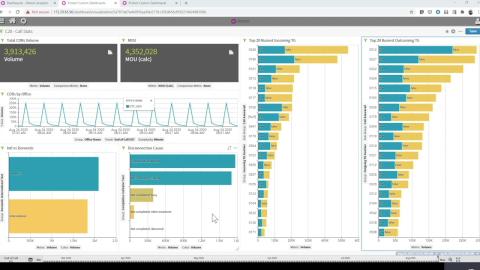
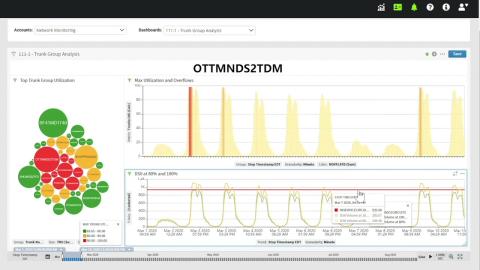
Powerful Visualization, Analyzing and Troubleshooting
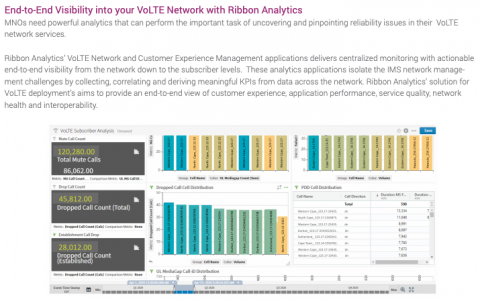
Service providers need powerful, flexible, and easy-to-use analytics tools to visualize and monitor network performance.
With Ribbon Analytics in your network, you will be able to monitor the network for KPIs and key trends as well as troubleshoot and alert on QoE issues. This provides many benefits such as end-to-end network visibility, improved operational productivity, and efficiency, faster troubleshooting, service issue identification, and resolution.
Read our Ribbon Analytics: Application Portfolio Solution Brief

Airtel Improves Customer Experience with Ribbon Mobile Network Analytics
Download Analytics Portfolio Solution Brief
Delivers a 360° understanding of IP data and real-time communications (RTC) usage enabling you to extract greater value for your end-users.
Quick Pro Tips
FREE professional tips to put you in charge of your voice network!
Voice Analytics for Mobile Network Operators
Effortlessly Scalable, Customizable, Unified view across the network
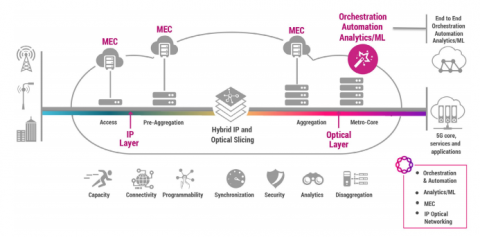
Ribbon’s voice analytics solution provides Mobile Network Operators(MNO) with scalable, customizable insights, that enable rapid issue resolution, revenue discovery, and improved customer retention. It supports 4G and 5G voice and multimedia services, including VoLTE (4G), VoWiFi, and VoNR (5G). Built as a modular analytics framework, it provides MNOs with the ease of deploying, maintaining and scaling the analytics platform to meet their growing needs. It uses a big-data, cloud native platform that underpins all its applications and solutions.
The Impact of Network Complexity
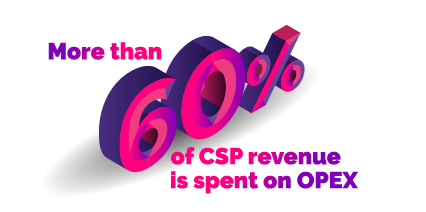
- Difficulty meeting SLAs and QoE requirements
- Reduced network visibility
- Inefficient operations
- Exposure to security attacks
- Reduced time to market
- Poor Customer experience
VoLTE / IMS Service Assurance
VoLTE / IMS Service Assurance
Watch his webinar to learn how Ribbon Analytics will bring you pre-defined and flexible analytics that can drive actionable insights from your VoLTE network. In this webinar, we will explain how MNOs are using Ribbon Analytics to:
- Distinguish network, application and device issues associated with poor subscriber experience
- Leverage analytics and machine learning to focus your staff on specific areas that are cause for concern
- Help to optimize investment decisions across their networks
Related Content
Learn more about Ribbon Analytics