Session Border Controllers for Dummies
Discover why you need a session border controller in your network.
Distributed Edge & Small to Medium Enterprises
Enterprise Data Center
Secure SBCs for Microsoft Teams Direct Routing
Secure Teams Direct Routing
Microsoft Teams Phone System and Direct Routing

Nice InContact Leverages Ribbon's SBC for SIP Peering

BMC transformed to a Hybrid Environment with Ribbon SBCs

Stone Brewing Pivots to Teams and Ribbon SBCs to Work from Home
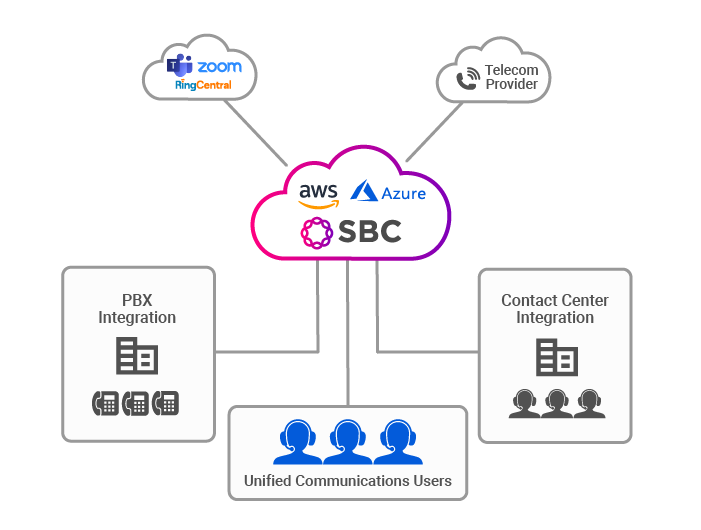
Ribbon Public Cloud SBC
Managing Ribbon SBCs

Ribbon’s SBCs are managed from a centralized Ribbon Application Management Platform (RAMP) offering a complete Fault, Configuration, Accounting, Performance, and Security solution. Delivering intuitive, reliable, scalable, and automated management, an enterprise can quickly configure multiple Ribbon SBCs, identify and remediate issues, deliver improved customer experience, and reduce operational costs.
Ribbon Application Management Platform manages SBC appliances, as well as software-based SBCS, deployed locally, in a private cloud, or public cloud. The platform itself is designed using cloud native principles and can also be deployed in multiple data centers and public or private cloud environments in standalone or high availability configurations, including options for geographic redundancy.
Download our RAMP Datasheet