-
Solutions
-
Service Provider Solutions arrow_forward_ios
- Service Provider Solutions Home
- By Service Provider Type arrow_forward_ios
- IP Routing and Optical Networking arrow_forward_ios
- Secure Cloud Communications arrow_forward_ios
- Metaswitch Migrations
-
Enterprise Solutions arrow_forward_ios
- Enterprise Solutions Home
- By Industry arrow_forward_ios
- IP Optical arrow_forward_ios
- Secure Cloud Communications arrow_forward_ios
- Critical Infrastructure arrow_forward_ios
- Mission Critical Defense arrow_forward_ios
-
Service Provider Solutions arrow_forward_ios
-
Products
-
Service Provider Products arrow_forward_ios
- Service Provider Products Home
- IP Routing & Packet Transport arrow_forward_ios
- IP & Optical Automation Platform arrow_forward_ios
- Optical Networks arrow_forward_ios
- Ribbon Acumen
- Analytics arrow_forward_ios
- Application Platforms & Clients arrow_forward_ios
- Call Controller arrow_forward_ios
- Identity Assurance arrow_forward_ios
- Cloud-Native IMS
- Media Gateways arrow_forward_ios
- Policy & Routing arrow_forward_ios
- Session Border Controllers arrow_forward_ios
- SS7 and Diameter arrow_forward_ios
- Enterprise Products arrow_forward_ios
-
Service Provider Products arrow_forward_ios
- Services
- Partners
-
Company
- About Us arrow_forward_ios
- Careers arrow_forward_ios
- Get Help arrow_forward_ios
- Investor Relations
- Media Center arrow_forward_ios
- Resource Library
- Sustainability arrow_forward_ios
-
Company arrow_forward_ios
- BABA Certifications
- Company Certifications
- Notices arrow_forward_ios
-
Policies arrow_forward_ios
- Information Security Policy
- Ribbon Academy Website Cookie Notice
- Corporate Biodiversity Policy
- Business Continuity Planning for Our Customers
- Business Continuity Policy
- Careers Cookie Policy
- Code of Conduct
- Cookie Policy
- Environmental Policy
- Privacy Policy
- Product Life Cycle Policy
- Quality Policy
- Responsible Disclosure Policy
- Responsible Procurement Policy
- Supplier Code of Conduct
- Statements arrow_forward_ios
- Terms arrow_forward_ios
- Support
-
Solutions
- Products
- Services
- Partners
-
Company
- Sustainability
-
Company
- BABA Certifications
- Company Certifications
- Notices
-
Policies
- Information Security Policy
- Ribbon Academy Website Cookie Notice
- Corporate Biodiversity Policy
- Business Continuity Planning for Our Customers
- Business Continuity Policy
- Careers Cookie Policy
- Code of Conduct
- Cookie Policy
- Environmental Policy
- Privacy Policy
- Product Life Cycle Policy
- Quality Policy
- Responsible Disclosure Policy
- Responsible Procurement Policy
- Supplier Code of Conduct
- Statements
- Terms
- Support
Lottie file
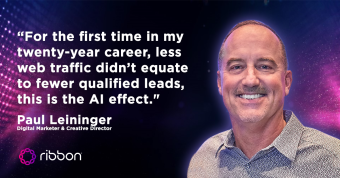
Ribbon Blog
Lottie file
Take the Next Step!
Lottie file